Developing your own encryption system is costly and labour-intensive. It requires a thorough understanding of current encryption best practices, the various encryption systems available, and forces you to choose between publicly available systems and more-secure private options.
Cloud Softphone is already being used to protect the European Union government from wiretapping and by private corporations who understand the importance of end-to-end encryption. You can easily add advanced encryption functionality to any app that you design through our platform.
Why Choose Acrobits’ Award-Winning Encryption Libraries
Cloud Softphone has everything you need to provide your users with the end-to-end encryption that they expect. Our advanced encryption libraries are available to anyone that designs their app using Cloud Softphone or our SDK.
Trusted by the European Union
Acrobits has developed its own proprietary encryption libraries that provide the
same level of security trusted by the European Union and which offer enhanced privacy and security functionality to private corporations around the world. Acrobits leverages ZRTP, SRTP, and TLS encryption to keep private user data safe through every stage of the communication process, from the initial client-side hello, to the handshake and the establishment of a secured connection between users.
A Safer Encryption Stack
Unlike other publicly-available encryption libraries, ours was developed privately and is unavailable to the public. Additionally, our ZRTP implementation was completed under the watchful eye of PGP creator and security expert Phil Zimmermann.
Best in Class Security
In
2017, German forensic researchers ranked the Acrobits SIP library as one of the most secure available in the world, placing it above Signal, Linphone, Jitsi, and CSipSimple. Their findings concluded that our technology, along with Signal, was the only client that protected against shared MitM attacks.
Prioritize Secure Communications to Protect Against Common Vulnerabilities
A vulnerability is any aspect of your organization that creates an opportunity for a cyber attack. Technologies involved in telecommunications have rapidly grown, but without the protections in place, each new device and technology can introduce a new vulnerability. A few common examples are:
- Internet of Things (IoT) Vulnerabilities: Every industry has seen an explosion in IoT devices used throughout their company. Whether used to improve infrastructure monitoring or directly provided to end users, IoT devices can provide powerful benefits. However, without strong encryption, they create an attack vector for malicious actors to exploit.
- Man-in-the-Middle (MITM) Attacks: This specific category of cyberattacks can target any system and it’s a common way cybercriminals attempt to compromise telecom networks. A MITM attack involves a malicious attacker positioning themselves between end-users and an application. From there, they can eavesdrop and siphon data or directly impersonate your systems for a range of malicious activities. Acrobits ZRTP protocol guards against this type of attack.
- Service Misconfigurations: Misconfigured hardware and software that allow for a wide range of attacks, generally by creating opportunities for attackers to bypass your firewall. Encryption is an important aspect of properly configuring your entire network and identifying any other misconfigurations that may enable a detrimental vulnerability.
- Third-Party Vulnerabilities: Your vendors, partners, or clients introduce a range of vulnerabilities when their systems or permissions are compromised. A malicious actor trying to target your system may look to your partners for a backdoor. Strong encryption is your first line of defence against many of these vulnerabilities.
Adopting an encrypted smartphone guard against several vulnerabilities to protect your data. You may still need advanced protections on top of encryption, but leading-edge encryption is the foundation of other cybersecurity practices.
Secure communications are a must-have to bolster your cybersecurity posture. You’ll likely still need to assess other risks and implement mitigation strategies, but adopting an encrypted softphone is a step in the right direction.
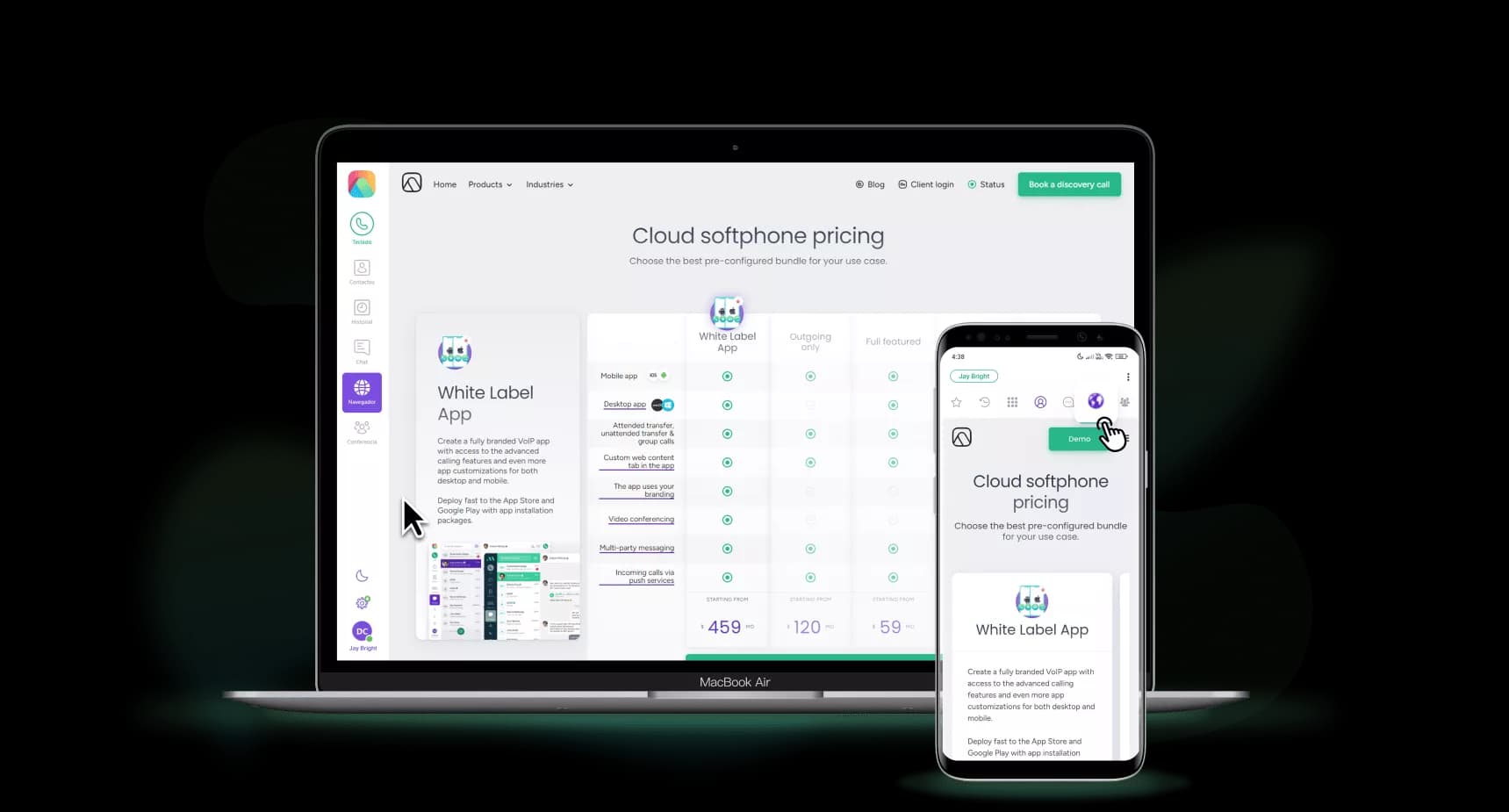
Cloud Softphone: Combine Functionality and Advanced Encryption
With Acrobits as your partner, you will have access to one of the deepest feature sets and most secure encryption libraries on the market. We make it easy for you to build the platform your business needs, without compromising on privacy and security with our
white label softphone platform.
Secure communications are essential, and Cloud Softphone was built with this in mind. We help companies like yours encrypt your voice and video communications, so you can offer the exceptional customer experience that your users demand.
Our security features include:
- • Peer-to-Peer Secure Voice and Video: Protect your users and their conversations from wiretapping and other forms of communications hijacking with our secure peer-to-peer voice and video functionality.
- • Man-in-the-Middle (MITM) Attack Prevention: Our ZRTP key agreement protocol is exactly what you need to prevent MITM attacks.
- • Encrypted Signalization: Verify the confidentiality and integrity of all signalization messages sent through your app with our advanced signalization encryption.
- • Encrypted Media: Our ZRTP encryption uses the Diffie-Hellman key exchange protocol to deter unwanted forces from accessing your user’s media.
With the majority of your competitors offering secure communications, you need to prioritize privacy and security in your mobile applications. Cloud Softphone makes it easy for you to build a secure mobile app.
If you’re ready to build a feature-rich platform that includes sophisticated encryption, contact us today to arrange an in-depth demo.